Critical Cybersecurity Strategies for Database Protection against Cyber Attacks
Abstract
In the realm of
Database Administration (DBA), it is paramount to ensure the security of
databases and servers. Protecting databases from cyber threats is critical for
maintaining data integrity and confidentiality. This paper will explore robust
strategies for safeguarding databases through advanced techniques and
procedural measures, such as implementing encryption protocols and securing
communications with SSL and TLS.
Furthermore, we
will emphasize the importance of continuous database monitoring utilizing tools
such as Idera, Datadog, and CrowdStrike. Collaboration with cross-functional
teams is essential in fortifying defenses against cyber-attacks; for instance,
the network operations team can enforce firewall configurations, system
administrators can conduct regular server patch management, and the security
team can implement multi-factor authentication (MFA) alongside periodic
Security Operations Center (SOC) audits. By reinforcing these enhancements,
organizations can effectively mitigate risks associated with unauthorized
access, minimize potential data breaches, and protect against ransomware
attacks, thereby ensuring the resilience of their database architecture and
safeguarding critical data assets.
Keywords: Cyber, SSL,
TLS, encryption, MFA, Datadog, proxy, ransomware, threats, access controls
1. Introduction
Datacenters serve
as crucial infrastructures for organizations, serving as the repositories for
their databases and servers. Cyber adversaries frequently exploit databases,
seeking to infiltrate these systems, which can result in significant data loss,
financial repercussions, and reputational harm. Prominent vulnerabilities
include SQL injection attacks, unauthorized access exploits, ransomware
incursions, inadequate encryption protocols, deficient access control
mechanisms, security flaws stemming from unpatched software, and nefarious
actions by insider threats.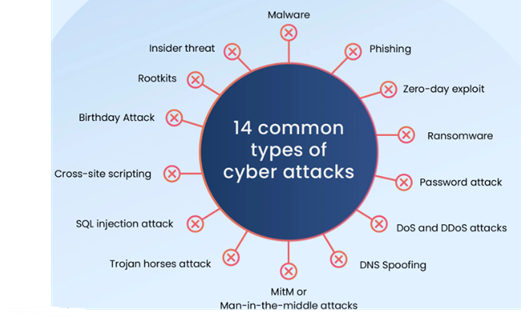
Figure
1: Common types of cyber attacks.
Databases are
integral to organizational operations, serving as the repository for critical
information vital for informed decision-making. However, these essential data
assets face escalating threats from cyber intrusions, which can lead to data
breaches, financial detriment, and reputational damage. To protect sensitive
information, organizations must deploy comprehensive cybersecurity strategies
tailored to the unique vulnerabilities inherent in database architectures. This
paper examines pivotal cybersecurity practices aimed at mitigating the risk of
cyber-attacks on databases, with a focus on advanced access control mechanisms,
data encryption standards, systematic patch management, and effective incident
response protocols. By comprehensively understanding and implementing these
strategies, organizations can significantly fortify their database security
framework, thereby safeguarding their invaluable data assets against malicious
threats.
2. Research
Background
This research
paper elucidates the challenges organizations face in securing databases
against an ever-evolving landscape of cyber threats. It underscores the
critical importance of prioritizing database security while also examining the
potential repercussions of negligence in this domain. Additionally, the paper
will propose future research directions aimed at enhancing database security
frameworks in collaboration with Database Administrators.
Database security
encompasses the methodologies, tools, and processes employed to safeguard
databases from cyber intrusions and unauthorized access. This involves
protecting the data housed within the database, the database management system
itself, and any applications interfacing with it. By adopting robust database
security protocols, organizations can avert misuse and preserve the integrity
of their data and systems. The overarching goal is to restrict access to
authorized users only, ensuring that sensitive information remains shielded
from cyber threats.
Several critical
factors concerning database security administration include:
- Massive
Data Processing: As organizations witness exponential data growth,
implementing cost-effective security measures for databases becomes
increasingly complex for Database Administrators.
- Heterogeneous
Environments: With the migration to cloud computing, data is
transitioning from on-premises datacenters to cloud environments. This shift
complicates the deployment, management, and selection of security solutions due
to the intricate nature of hybrid and multi-cloud architectures.
- Audits
and Compliance Landscape: Conducting audits across extensive data
landscapes presents significant challenges, necessitating that DBAs leverage
automation and artificial intelligence techniques to generate accurate audit
results, a process that can be time-consuming.
- Shortage
of Cybersecurity Expertise: A
global deficit of skilled cybersecurity professionals’ hampers organizations’
ability to effectively shield critical infrastructure, including database
administration.
The following
research questions will guide the inquiry into database security practices that
Database Administrators must address:
- How can databases
maintain security during connections from external environments to data centers
or servers?
- What mechanisms
are available for routing IP addresses to access databases securely?
- Are there firewall
configurations that effectively mitigate unauthorized access to server and
database ports?
- How secure is
sensitive data during querying or visualization from applications?
- Is security
integrated into user-level permissions within the database?
- Have role-based
access controls been established to streamline database interactions?
- Should SSL, TLS,
or encryption protocols be implemented at the data, database, or network
levels?
According to a
study by Guardium, human error accounts for 95% of cybersecurity incidents,
highlighting the need for organizations to mitigate risks posed by inadvertent
security oversights.
The synergy
between database security and automation is paramount. The integration of
machine learning technologies and automated detection systems can facilitate
real-time identification of security vulnerabilities. By enhancing monitoring
and analytical capabilities, organizations can reduce false positives while
improving their response to genuine cyber threats.
By leveraging
automation in database security, teams can allocate resources toward other
critical tasks while maintaining continuous protection. Furthermore,
intelligent automation can streamline the management of security patches,
minimizing human error, time expenditure, and operational costs.
2.1.
AI integration research
The integration of
Artificial Intelligence (AI) is revolutionizing database security management.
AI technologies enable enhanced threat detection, optimize incident response
procedures, and identify anomalous behaviors within database systems.
- Investigate how AI can reinforce database security
administration against cyber threats.
- Analyze the
potential risks and vulnerabilities that may arise from incorporating AI into
database security architectures.
AI Tools for Database Security Enhancement: Tools such as
CrowdStrike Falcon, Sentinel One Singularity, McAfee Enterprise Security
Platform, Palo Alto Networks Cortex XDR, Darktrace, and IBM QRadar are leading
the charge in this domain. These solutions typically offer features such as
Threat Protection, AI-Driven Detection, and Real-Time Visibility into database
environments.
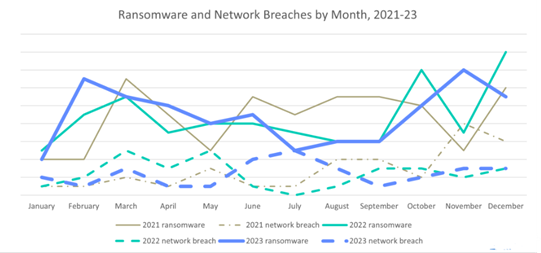
Figure
2: Trends in Ransomware Extortion Breaches
Over Time.
Figure
3:
Phishing Email Report Rates Based on Click Status.
3. Approach
to Ensuring Database Security: A Methodological Framework
Some of the major
methodologies need to be followed for database security with the help of an administrator,
here are the good strategies to avoid data breaches.
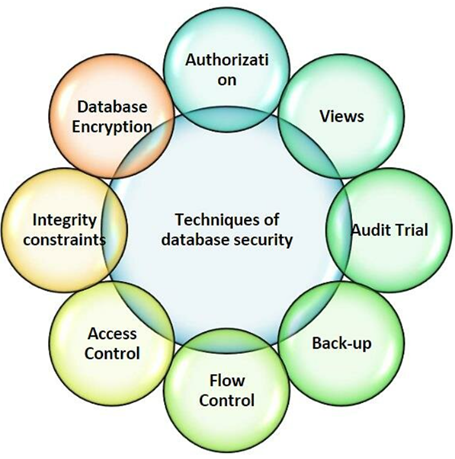
Figure
4:
Database Security Workflow: A Comprehensive Flow Process
3.1. Private
network configuration
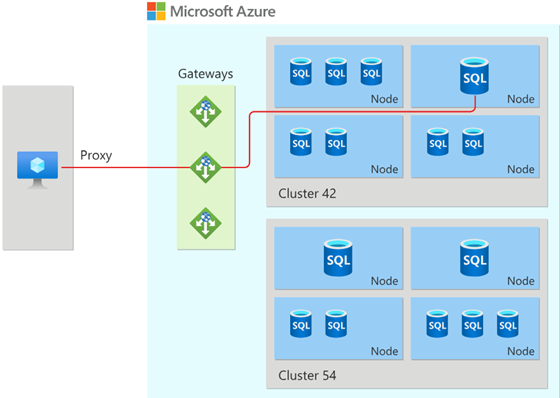
All database
servers should be housed within a private network architecture to prevent
unauthorized public access. This configuration ensures that public interactions
with the database servers are effectively restricted, while firewalls are
strategically deployed to filter and block unwanted IP addresses, bolstering
the overall security posture of the database environmen.
Figure
5:
Azure SQL Servers: Configuration within a Private Network.
3.2.
Proxy server
A database proxy
operates as a mediator between client applications and the database management
system, enhancing communication efficiency and fortifying security measures.
When a database access request is initiated, the proxy intercepts and processes
it, executing critical functions such as load balancing, connection pooling,
transient data caching, and query optimization. One of the primary advantages
of integrating a database proxy is its capacity to diminish the number of
direct connections to the database, which leads to improved performance and
mitigates the risk of server congestion. By effectively managing a pool of
persistent connections and reusing them as necessary, the proxy alleviates the
operational overhead associated with repeatedly establishing and terminating
connections, thereby facilitating a more efficient and seamless database
operation.
Figure
6:
Proxy Workflow: Visualizing the Process
of Accessing Databases.
3.3.
Backup strategies
Regular database
backups are critical for ensuring data integrity; however, it is essential to
also implement robust protection for these backups, as they can become prime
targets for cyber attackers. This is particularly vital for organizations that
handle sensitive customer data, such as healthcare providers and financial
institutions.
Backup Validation:
Regular validation of backups is crucial for ensuring their security and
reliability.
Ransomware
Mitigation: Employing tools like Clumio can enhance the
resilience of database backups against ransomware threats.
3.4.
EncryptionEncryption serves
as a mechanism for transforming data into an encoded format, rendering it
unreadable without the appropriate decryption key. SQL databases offer various
encryption methodologies, each with distinct features and applications tailored
to specific use cases in data security and compliance.

Figure
7: Encryption Workflow: A Visual Representation of the
Data Encryption Process.
3.5.
Monitoring
Continuous
monitoring of databases is essential to promptly identify and address any
issues that may arise. Utilizing tools such as Idera and Datadog, along with
automated alert configurations and CloudWatch alarms, can facilitate real-time
notifications of potential anomalies.
3.6.
SQL injection
SQL injection
represents a database-specific vulnerability where malicious actors exploit
faulty input in SQL queries to manipulate the database into executing
unauthorized actions. This threat is prevalent in web applications when users
submit invalid data through forms. Any database can be susceptible to SQL
injection attacks if developers fail to adhere to sound coding practices and
organizations do not conduct regular security assessments.
3.7.
Firewall protection
Implementing a
firewall is crucial for safeguarding the database server from external threats.
By default, a firewall blocks all inbound traffic; therefore, it is advisable
to strictly control database connections unless there is a legitimate
requirement. In conjunction with a traditional firewall, a Web Application
Firewall (WAF) is also necessary, as it provides an additional layer of defense
against web-based attacks, such as SQL injection, which can compromise
databases.
It is important to
note that a database firewall operates at a different layer and may not
effectively mitigate website attacks, whereas a WAF operates at an application
layer, capable of detecting and mitigating malicious web traffic before it can
affect the underlying database.
3.8.
User authentication
Effective database
security hinges on robust user authentication practices to regulate access for
users and applications. Recommended security measures include:
- Enforcing strong
password policies.
- Ensuring password
hashes are salted and stored in an encrypted format.
- Locking accounts
after a specified number of failed login attempts.
- Conducting regular
account reviews and deactivating access for individuals who transition to new
roles, exit the organization, or no longer require equivalent access levels.
3.9.
Multi-factor authentication (MFA)
One of the most
effective security strategies today is the implementation of Multi-Factor
Authentication (MFA). This method sends a notification or message to the user’s
mobile device, requiring authentication before allowing applications or users
to connect to the designated servers.
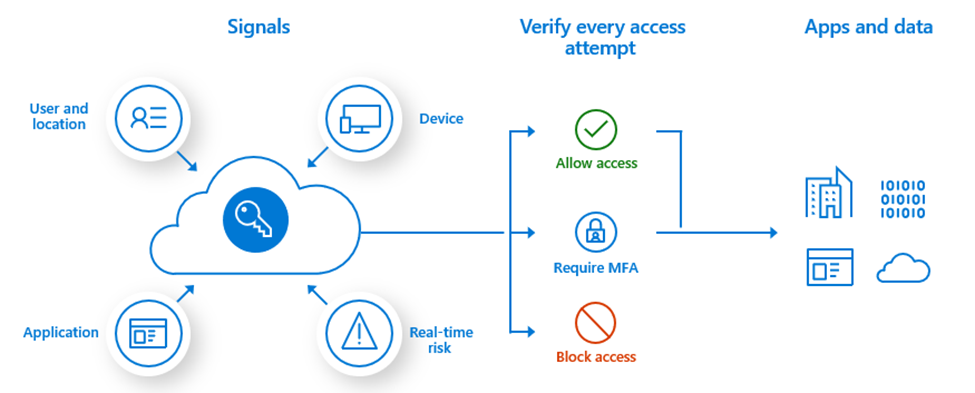
Figure
8: MFA Authentication.
3.10. RSA token
An RSA token is a
security device that enhances login authentication by requiring a unique code
generated by the token in addition to the user’s password. This two-factor
authentication mechanism significantly reduces the likelihood of unauthorized
access to accounts.
3.11.
Vulnerability remediation
Regular
remediation of vulnerabilities is essential in maintaining database security.
Tools like IBM Guardium provide comprehensive reports that assist the database
administration and audit teams in identifying and addressing potential security
weaknesses.
3.12.
Comprehensive audits
Conducting
thorough audits is critical for assessing the security of customer data. SOC 1
and SOC 2 audits are essential for databases to identify and mitigate any
security issues effectively.
3.13. Denial of service
(DoS) attacks
A Denial of
Service (DoS) attack occurs when a database server is inundated with excessive
requests, causing the system to become unresponsive. These requests, often
generated by attackers, can overwhelm the system, leading to service
disruptions. A Distributed Denial of Service (DDoS) attack is an escalated form
of this threat, leveraging a vast network of compromised computers to flood a
target with traffic, which can be challenging to mitigate, even with advanced
security measures in place. The most effective defense against such attacks is
to utilize cloud-based services designed to detect and manage suspicious
traffic.
3.14. Patching
Regularly patching
databases and servers is crucial for keeping security measures current and
optimizing performance. Research indicates that 88% of codebases contain
outdated software components. Furthermore, deprecated plugins serve as prime
targets for malware exploitation, creating significant vulnerabilities that
hackers can leverage to access other areas of the network. This scenario
presents substantial security risks related to the software utilized for
database management and web operations.
4.
Consequences of Database Breaches
Database breaches
pose significant threats to both organizations and individuals, resulting in
severe repercussions that include financial losses, reputational damage, and
legal complications. Organizations that experience the loss of customer data
can suffer erosion of trust and customer attrition. Moreover, they may face
substantial fines and legal liabilities, particularly within regulated sectors
such as finance and healthcare. The ramifications extend to individuals as
well, whose personal information may be compromised and exploited for
fraudulent activities.
The cumulative
impact of these issues can hinder organizational growth and operational
success, underscoring the critical need for robust database protection against
cyber threats. According to IBM's annual Cost of a Data Breach Report, the
global average financial impact of data breaches in 2024 has reached an
alarming $4.88 million.
5. Future
Research and Enhancements
The implementation
of high availability and disaster recovery frameworks, including automated
backup solutions and fault tolerance strategies, is essential for ensuring
database accessibility and enabling rapid data restoration in the event of a
breach or system failure.
The integration of
Artificial Intelligence (AI) and automation can significantly reduce costs
associated with database security management. Machine learning algorithms can
facilitate the analysis and remediation of security detections while providing
predictive insights into future threats and vulnerabilities. Furthermore,
developing best practices for securing databases within cloud environments is
crucial, particularly with regard to considerations such as multi-tenancy, data
isolation, and stringent access controls.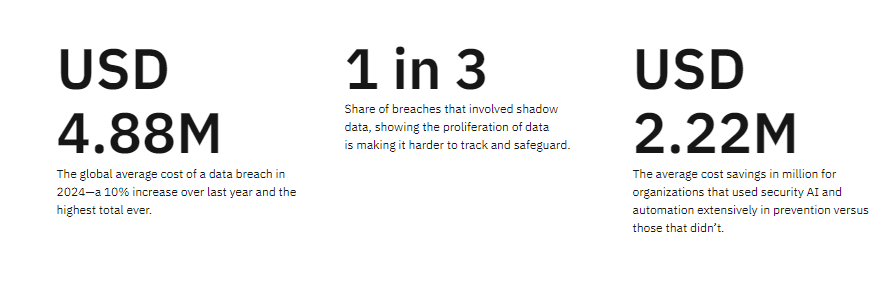
Figure
9: Leveraging Security AI and Automation to Reduce
Breach Costs, According to IBM.
6.
Advantages of Best Practices
The following
preventative measures can effectively mitigate your database's exposure to
cybersecurity threats:
- Enhanced employee
training to ensure the consistent application of security best practices.
- Conducting a
thorough assessment of the attack surface associated with your network and
database systems.
- Implementing a
zero-trust security architecture to minimize risk.
- Disabling inactive
accounts and restricting user privileges for standard access levels.
- Employing
encryption for both the database and all backup copies.
- Blocking
potentially harmful web requests to safeguard against attacks.
- Monitoring
database access and analyzing user behavior patterns to detect anomalies.
- Utilizing data
masking techniques to obscure sensitive information within database fields.
7.
Conclusion
It is imperative
for organizations of all sizes to safeguard their databases against cyber
threats. Successful breaches can lead to severe consequences, including data
loss, financial damage, and reputational harm to the organization. By adopting
robust security protocols, businesses can significantly enhance their defenses
against potential attacks on their databases. Implementing these critical
cybersecurity measures will empower organizations to substantially lower their
risk of data breaches and protect their valuable information assets. Moreover,
it is essential to remain vigilant regarding emerging threats and continuously
assess and refine security strategies to ensure sustained protection in an
ever-evolving cyber landscape.
8. References
- Database
Security: Principles and Practice by Peter Aiken and David Stewart.
- Securing
Databases: A Guide for IT Professionals by Michael G. Fitzgerald.
- Database
Security: A Comprehensive Guide by Jim Reavis and Mike Riley.
- https://www.esecurityplanet.com/networks/database-security-best-practices/
- Tripwire
- Database Security Best Practices.
- Synoptek
- The Top 5 Cybersecurity Measures to Take in 2024.
- https://www.nist.gov/cybersecurity-framework
- https://www.cisa.gov/topics/cybersecurity-best-practices