Mitigating Escalating Cybersecurity Threats in advanced Automotive Systems
Abstract
With the rise of connected cars and their integration with various networks and systems, there is a higher risk of cyberattack targeting these vehicles. Hackers can exploit vulnerabilities in the car’s software or network to gain unauthorized access and control over critical functions. This scholarly article explores into the escalating challenges, vulnerabilities and defense measures essential for safeguarding intelligent connected vehicles against cyber threats.
Keywords: Connected Vehicles, Cybersecurity, Connectivity, CAN (Controller Area Network), Autonomous, V2X, Artificial Intelligence.
1. Introduction
Vehicle OEMs and their suppliers are integrating increased connectivity features with an objective to provide enhanced safety and user experience for their customers. Many advanced technologies, such as artificial intelligence, V2X (Vehicle to everything), OTA (Over the Air) updates, cloud computing, online subscription features and ADAS (Advanced Driver Assistance Systems) are widely being used in the cars, which makes connected vehicle more intelligent to provide comfortable services for people but at the same time the risk of cyber-attacks has become a growing concern.
Factors contributing to increased Cybersecurity risks in automotive and their counter measures:
1.1. Cyber vulnerabilities overview:
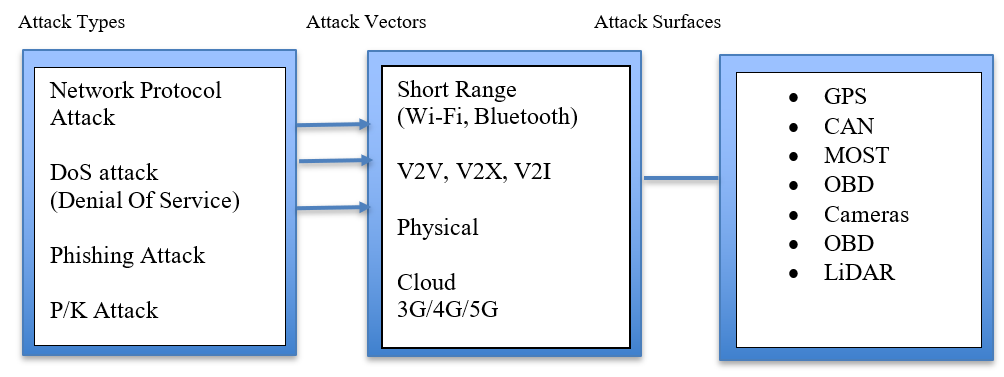
Figure 1: Overview of cyber-attack types, attack vectors and attack surfaces
1.2. Vehicle Networking Protocols
MOST (Media Oriented System Transport): This network is used for media and infotainment and is less harmful as it is not directly connected to critical systems like Power train or engine related sensors. However, two types of attacks are possible on MOST, synchronization disruption and jamming. In synchronization attacks, hacker can send the fake timing frames continuously and tamper the synchronization of MOST. Whereas in jamming, hacker can send the misleading messages and interrupt low priority legitimate messages1.
Counter Measures: Source code authentication, encryption of exchanged messages and strict enforcement of firewalls can be considered to address above threats.
- CAN (Controller Area Network) & Flex ray:
Most of the ECUs (Electronic Controller Units) in the vehicle are connected to the vehicle CAN and Flex Ray networks. These network protocols lack design of an information security mechanism at the beginning of its design which makes them vulnerable to sniffing, replay or forgery of messages. The CAN message has poor confidentiality, the bus data is easy to capture and analyze and the availability and integrity cannot be guaranteed. There is no original address information in the CAN message which makes it easy for the attacker to tamper with the message by injecting false information. Also, the arbitration mechanism given priority in the CAN bus protocol which can make attacker replay or flood the vehicle bus by means of sniffing. - OBD (On Board Diagnostics) port is used for vehicle diagnostics and for ECU software updates. In this case, diagnostic tool can gain access to vehicle network over the CAN bus. This can be hacked by installing malware through direct connection.
Counter measures: Researchers have explored Security enhancement technologies for vehicle networks, which include,
1.3. Vehicle network data encryption technology2
Here, the security solution of the CAN bus can be divided into encryption, authentication and redesign of protocol stack.
Cryptography-based methods focus on protecting the CAN bus from malicious messages, while the intrusion detection system (IDS) focuses on detecting malicious messages.
Firewalls and intrusion prevention systems (IPS) can be considered for external interfaces to prevent access to the bus.
1.4. Vehicle Network Message Authentication Technology
A variety of lightweight message authentication protocols can be considered to protect vehicles from camouflage attacks.
1.5. Vehicle network Intrusion Detection Technology
This is more suitable for vehicle networks with limited resource and cost. This detection technology is further categorized into detection methods based on feature observation, information theory, statistical analysis and machine learning etc2.
- Vulnerabilities in Smart key systems: These systems eliminate the need for a physical key by depending on wireless communication between the vehicle and the key fob but may become vulnerable to cyber enabled replay attacks (Signal replication by malicious actors leading to vehicle theft).
- Counter measure: Tesla tried to overcome the issue by replacing traditional RKE (Remote less Key Entry) design with Bluetooth Low Energy (BLE) enabled key, however, this design too was vulnerable to relay attack and it was defeated by cost issues. The other countermeasures considered are rolling code3 and separating the door control and engine unlock functions to avoid the problem of simply opening the door to drive the vehicle away.
- Connected and autonomous Vehicles (CAV): V2X communications involves communication between Vehicle-to-Vehicle(V2V), Vehicle-to-Infrastructure(V2I), Vehicle-to-Pedestrian(V2P) and V2R (vehicle-to-roadside units). This communication is facilitated by VANET technology (Vehicular ad hoc networks). The cyber-attacks and counter measures in V2X communication is categorized into,
1.5.1. Attacks on authentication: Authentication defines the ability to verify the legitimate sender of the message. The absence of strong authentication mechanism had led to threats such as GPS spoofing and masquerading attacks. Researchers have suggested potential prevention and mitigation techniques which include encryption, location algorithms, cryptography and artificial intelligence.
1.5.2. Attacks on availability: Availability defines that the authorized users shall have all the time access to network resources. Common attacks on availability include denial of service (DOS) attacks, jamming attacks, black and grey hole attacks. Studies on these attacks provided mitigation and detection mechanisms such as monitoring, packet detection and machine learning methods4.
1.5.3. Attacks on integrity: Integrity confirms that the message has not been modified along the communication channel. Attacks on integrity include replay and false injection. Suggested prevention algorithms on these kinds of attacks include cryptography, timestamp verification, message verification and machine learning.
1.5.4. Attacks on non-repudiation: Non-repudiation means accountability. Any action performed on the network must be accounted for. In a repudiation attack, it is impossible to identify the sender of a message on the network. To address this concern, the authors use digital signatures, mutual authentication and certificate authorization techniques. More studies to ensure accountability while maintaining the privacy have been performed.
1.5.5. Attack of Confidentiality: Confidentiality protects the content of the messages from unauthorized access by the users. This kind of attacks include eavesdropping, man-in-the-middle attacks. Kalman filtering and deep reinforcement learning techniques have been suggested by the researchers to address this attack.
1.5.6. Attacks on Privacy: This includes protection of data such as identity of the user and position details of the sender. To address this security attack, studies suggested tree-based risk assessment, cryptography, location cloaking and encryption-pseudonyms.
The above discussed countermeasures, such as cryptography and Intrusion Detection Systems (IDS) are highly effective for preventing and detecting external attackers but less effective in internal attack situations. Also, these techniques are computationally expensive and limited to known attacks. To address these challenges, focus on research is turned towards evaluating credibility of sender and message through trust. Numerous studies such as Fuzzy logic, game theory, block chain, RSU based, cloud and edge assisted frameworks have been done to improve the internal security of connected and autonomous vehicles using trust-based security solutions, however, there are some drawbacks and require further research to enhance security in connected and autonomous vehicles.
Cloud based services: OEMs and suppliers offering functionalities such as remote command execution and vehicle status monitoring to vehicles, represent another potential weak point in the automotive data ecosystem.Also, vehicles now regularly communicate with OEM and third-party cloud services for over-the-air updates and subscription. This expanded connectivity significantly increases the vulnerability to cyber-attacks.
In 2022, a vulnerability was identified in the MQTT broker of the HQT-401 telematics unit, which lacked required authentication mechanisms. This flaw allowed attackers to manipulate the telemetry data5. In another instance, the lookout for vehicle data leaked via MQTT revealed several open brokers, lacking both authentication and password protection. Many unsecure MQTT servers accept write instructions from any subscriber which opens the potential for attacks.
Over the air technology helps automakers and users to avoid physical visits to the dealership by updating the software in the vehicle from remote over the cloud servers6. But this technology, introduces potential vulnerabilities regarding the authenticity and integrity of the updates.
Cloud based Subscription management has transformed revenue models for OEMs and suppliers however, this helped attackers to generate revenue by jailbreaking the features and avoiding the subscription fee.
Counter measures: A cloud API is the main character of the whole network architecture that provides variable functions.
More secure API should be developed considering good practices, (1) Address AuthN (2) Following least privilege model (2) Adopt data minimization (4) Avoid incremental IDs (5) Enforce rate limiting (6) Sanitize inputs and reject anything suspicious (7) implement proper security headers (8) Configure CORS to reduce attack surface (9) Don’t reveal useful info in error messages (10) Use versioning and deprecate old APIs. Also, Cybersecurity cannot be one time testing, it shall be part of the active SDLC (Software development life cycle) and security design and implementation shall run in parallel with software development lifecycle.
AI driven driver assistance and autonomous driving systems: Autonomous vehicles are susceptible to malicious interference. AI and ADAS (Advanced Driver Assistance Systems) depend on several sensors, cameras and algorithms to interpret the environment and make decisions. Generally, ADAS systems use sensors for capturing the inputs, interpret the input data using the AI models and then use actuators for driving the outputs. Sensor data, especially, camera inputs, are vulnerable to attacks, for instance, when IR (Infrared) light is directed by the camera sensors, it can be misinterpreted as red signal, causing vehicle to perform unintentional breaking, called ghost breaking7.
AI provides plenty of opportunities to address cyber security threats which include,
AI supported Intrusion Prevention Systems: This helps to analyze large amounts of data from various sources in real time to identify emerging threats, analyze attack methodologies and provide real-time threat intelligence reports. This allows cybersecurity experts to become more proactive and strengthen security measures before attacks happen.
AI supported IDS (Intrusion Detection Systems): IDS can analyze large amounts of data in real time (1) identify suspicious activities (2) Analyze network traffic (3) Provide timely warnings to security teams. This helps to continuously learn from new threat patterns to update its algorithms.
AI can prevent attacks by analyzing messages through natural language processing to detect phishing attempts by recognizing (1) Suspicious patterns (2) misleading information and (3) malicious URLs.
On the flip side, however, AI systems themselves can become targets for hackers. Adversarial attacks, where small manipulations in data can cause AI systems to make incorrect decisions, present a significant risk. For instance, researchers demonstrated how slightly altered stop signs could cause Tesla’s Autopilot system to misinterpret them, showing how vulnerable AI can be to carefully crafted attacks.
Also, AI can help attackers by gathering information about the target, educating the attacker on needed equipment and how to perform certain attack actions and help writing malicious code. It benefits reduction in attack times and provides needed expertise with ease. AI can help attackers with searching data easily to enhance the attack, creating phishing emails and creating Deep fakes. AI (specifically chatbots) can also create polymorphic malware which is very hard to detect.
Counter measures will be needed to control the rising threat of AI generated or enhanced attacks. AI systems are expected to become more adept at predicting and preventing attacks through continuous learning and adaptation. Companies are exploring the integration of quantum computing which will strengthen AI capabilities by building unbreakable encryption methods and rapid detection of threats. Collaborative efforts of auto industry are needed to establish standards and protocols. AI shall continuously monitor and ensure regulatory compliance in automotive industry.
2. Conclusion
This article explores the several security breaches that can happen at any interface of the vehicle architecture, it can happen anywhere between vehicle communication bus protocol level to the application level, which include interfaces to the cloud, other vehicles and external infrastructure. Initially automotive protocols are designed without considering the security threats, but current scenarios require advanced security measures for these protocols to counter against malicious attacks. Researchers are exploring Vehicle network Intrusion Detection Technology which is suitable for vehicle networks with limited resource and cost. Also, in case of CAV (Connected and autonomous vehicles), the researchers are exploring trust-based frameworks to address internal type attacks as IDS helps addressing external type attacks. Also, the cloud-based attacks were discussed and the factors to be considered while developing APIs were mentioned. Connected vehicle technology will rapidly change with the rapid transformation of AI. Vehicle connecting to external world (Cloud, other vehicle and infrastructure) is changing rapidly. To maintain safety and security while increasing the number of connected vehicles functions the automotive industry, academia and government bodies need to be aligned, especially in terms of safety standards. As technology advances, safety standards and regulations should be reviewed and updated as appropriate.
Design, implementation and testing of Security methods should be an active part of the SDLC (Software development Lifecycle) and shall run in parallel with the software development lifecycle instead of giving emphasis to security at the later stage of the development cycle.
3. References
- Rathore RS, Hewage C, Kaiwartya O, Lloret J. In-Vehicle Communication Cyber Security: Challenges and Solutions. Sensors, 2022;22:6679.
- https://www.mdpi.com/2071-1050/14/9/5211
- https://vicone.com/files/rpt-automotive-cybersecurity-in-2022.pdf
- https://ietresearch.onlinelibrary.wiley.com/doi/10.1049/itr2.12504
- https://nvd.nist.gov/vuln/detail/CVE-2023-3028
- Numaan Huq M.Sc. Automotive Cyber Security - Emerging Risks and New Case Study Insights: ATZ Electronics, 07-08:2024
- https://www.reddit.com/r/SelfDrivingCars/comments/10gngs6/ghost_braking_incidents_threaten_usefulness_of/